|
February, 2014 Tech and Law Center interviews Jesse Kornblum, Security Engineer for Facebook. Based in the San Francisco Bay area, his research focuses on computer forensics and computer security. He has helped pioneer the field of memory analysis and authored a number of computer forensics tools. These tools include the Hashdeep suite of programs and the ssdeep system for fuzzy hashing similar files. A graduate of the Massachusetts Institute of Technology, Mr. Kornblum previously served as a computer crime investigator for the Air Force and with the Department of Justice. Twitter When did you become interested in digital forensics? Was there any particular event that triggered your interest?
What is your opinion on certifications and education in the forensics field? What improvements would you make?
What can we expect when it comes to malicious code on mobile devices? Are there any interesting things that people need to be aware of?
Storage capabilities of todays system are increasing at a very high pace. How is it possible to manage in an efficient and comprehensive manner the huge amount of data that have be analyzed?
Which will be, in your opinion, the challenges that Digital Forensics field will have to face in the coming years?
|
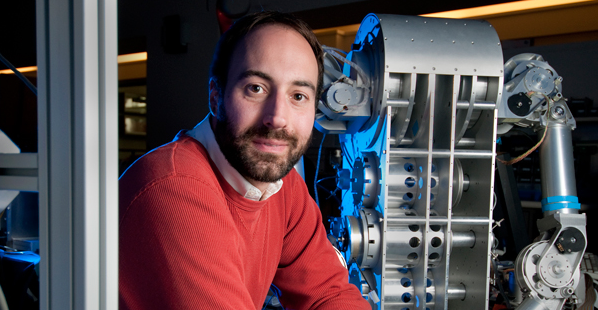
Jesse Kornblum
Inspiring websites
- Casinos Not On Gamstop
- Best Non Gamstop Casinos
- Non Gamstop Casinos UK
- Migliori Bonus Casino
- Casino Not On Gamstop
- Casino Not On Gamstop
- Casino Online Deutschland
- Best Non Gamstop Casinos
- Non Gamstop Casino UK
- Non Gamstop Casino Sites UK
- Casino Français En Ligne
- Sites Not On Gamstop
- Best Non Gamstop Casinos
- UK Casino Not On Gamstop
- Casino Sites Not On Gamstop
- Lista Casino Online Non Aams
- Gambling Sites Not On Gamstop
- Non Gamstop Casino Sites UK
- Non Gamstop Casino UK
- UK Casinos Not On Gamstop
- Top Slot Sites 2025
- UK Casino Not On Gamstop
- Casino Sites Not On Gamstop
- Casino En Ligne
- Non Gamstop Casino
- Non Gamstop Casino UK
- Casino Online Migliori
- Bitcoin Casinos
- Meilleur Casino En Ligne Français
- Sites De Paris Sportifs Belgique
- Casino Online App
- Casino Non Aams
- Casino En Ligne Fiable
- KYC 절차 없는 온라인 카지노
- 稼げるカジノアプリ
- Nouveau Casino Francais En Ligne
- Scommesse In Crypto
- Casino Senza Richiesta Documenti
- Migliori Crypto Casino
- Nouveau Casino En Ligne 2026
- Casino En Ligne Francais
- Crypto Casino
- Meilleure Casino En Ligne
- Casino Français Crypto
- Migliori Casino Non AAMS
- Meilleur Casino Sans KYC